Search the Community
Showing results for tags 'geoip'.
-
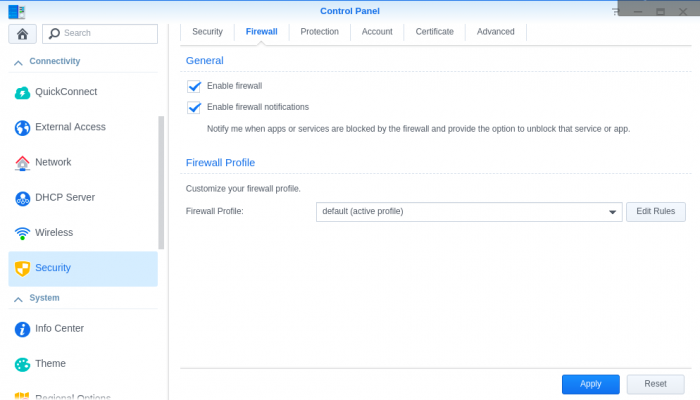
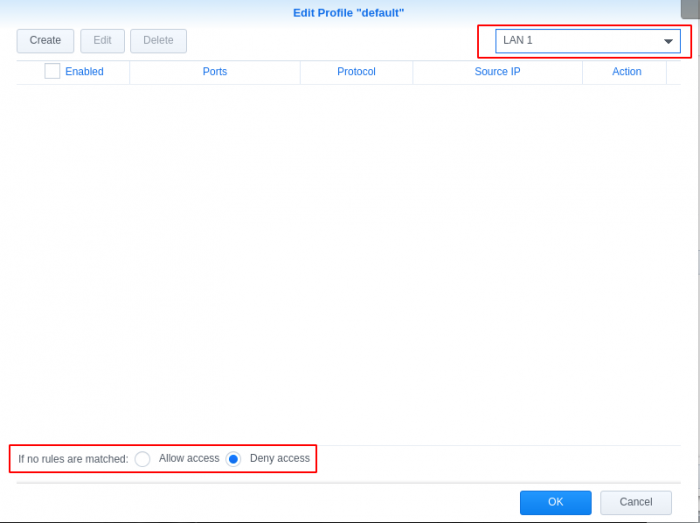
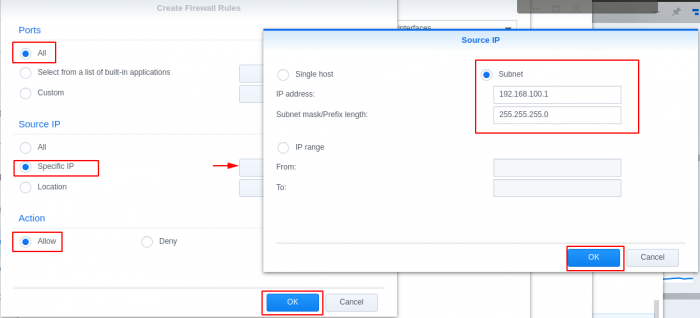
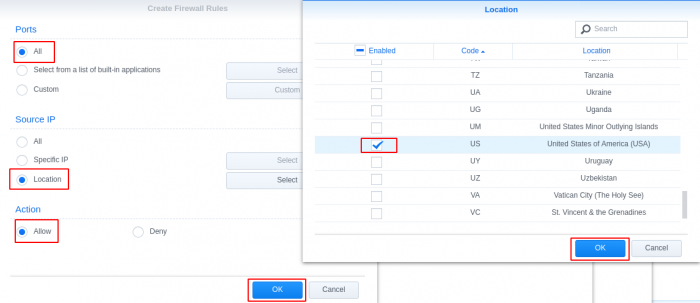
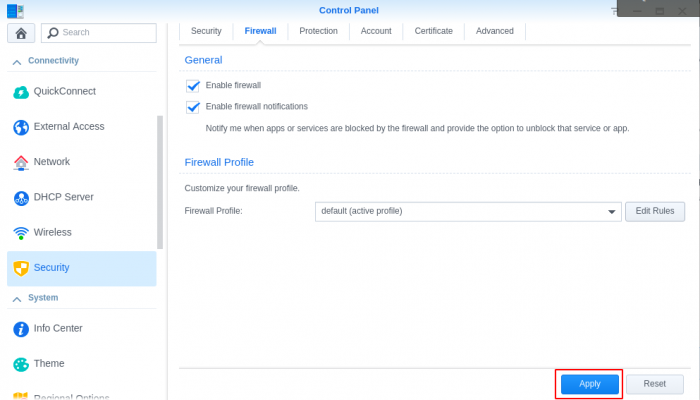
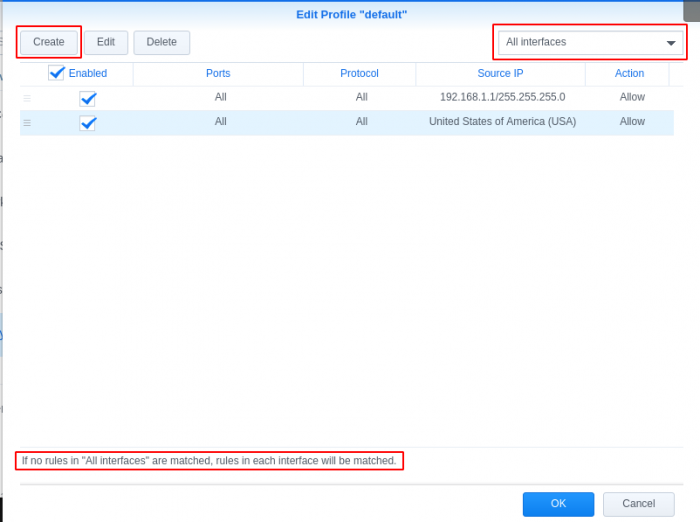
GeoIP Region Blocking using Synology Firewall I noticed internet performance issues today and was checking my router logs, I found excessive logs showing: Jun 18 20:55:48 dropbear[5405]: Child connection from <My Synology IP>:40894 Jun 18 20:55:49 dropbear[5405]: Exit before auth: Exited normally Jun 18 20:55:49 dropbear[5411]: Child connection from <My Synology IP>:40896 Jun 18 20:55:51 dropbear[5411]: Exit before auth: Exited normally I searched and found it was related to numerous invalid login attempts to the synology login page. This lead me to login to the cli of my synology and check logs for failed attempts. When checking the logs I found the most concerning log was /var/log/httpd/apache22-error_log 2018-06-18T19:28:42-06:00 nas [Mon Jun 18 19:28:42 2018] [error] [client 193.106.30.99] File does not exist: /var/services/web/wp-rdf.php 2018-06-18T20:11:16-06:00 nas [Mon Jun 18 20:11:16 2018] [error] [client 27.29.158.10] script not found or unable to stat: /var/services/web/login.cgi 2018-06-18T21:51:26-06:00 nas [Mon Jun 18 21:51:26 2018] [error] [client 172.18.0.2] File does not exist: /var/services/web/apple-touch-icon-precomposed.png 2018-06-18T21:51:26-06:00 nas [Mon Jun 18 21:51:26 2018] [error] [client 172.18.0.2] File does not exist: /var/services/web/apple-touch-icon.png 2018-06-18T21:51:26-06:00 nas [Mon Jun 18 21:51:26 2018] [error] [client 172.18.0.2] File does not exist: /var/services/web/apple-touch-icon-precomposed.png This lead me to consider blocking all geographical regions except my own. Most brute force attempts and vulnerability attacks are outside of my home country, this will reduce the attack surface significantly. My first attempt at implementing the geoip blocking was problematic, I attempted a "deny all" entry after the "allow local network range" and "allow my region" rules, but this ended up blocking all access to the services I had running. I thought I'd share how I implemented it for others wanting to reduce the surface area for attacks. Enable firewall Open Control Panel Select Connectivity -> Security Go to Firewall tab Check Enable firewall Add "Allow" Rules for internal network Select Edit Rules for the default Firewall Profile (Disregard existing rules in screen shot, these will be created in the following steps) Create rule to allow your internal/home network Add "Allow" Rules for your country/countries Create rule to allow specific locations Set network interface to deny if rules are not matched Select the network interface that is default to your synology (mine is LAN 1, you can find your interface under Connectivity -> Network -> Network Interface) ***This was the secret to getting the deny all after the allow rules to work*** Set "if no rules were matched: Deny Access" Click OK and Apply Test reaching your synology on your internal network and from external networks in your region. You can also validate if the firewall is blocking by using a Tor browser to send traffic from a different country to see if your firewall rules are working properly.